In the modern web landscape, where data breaches and cyber threats are increasingly prevalent, securing back-d applications has become a critical concern for developers. Node.js and TypeScript have emerged as popular choices for building scalable and efficient back-end systems. However, with their growing adoption, it's essential to implement robust security measures to protect sensitive data, mitigate vulnerabilities, and maintain the integrity of your applications. In this comprehensive blog post, we'll explore best practices for securing Node.js and TypeScript back-end applications, providing you with a solid foundation for building secure and resilient systems.
Implementing Authentication and Authorization
Secure Authentication Strategies
Proper authentication is the first line of defense against unauthorized access to your application. Node.js offers various authentication libraries and frameworks, such as passport.js, that provide a range of strategies for implementing user authentication. It's crucial to choose a secure authentication method, such as JSON Web Tokens (JWT) or OAuth, and to follow industry-standard practices for password hashing and salting.
Role-Based Access Control (RBAC)
After authenticating users, it's essential to implement authorization mechanisms to control what actions they can perform within the application. Role-Based Access Control (RBAC) is a widely adopted approach that assigns permissions based on defined roles. This ensures that users only have access to the resources and functionalities they require, reducing the risk of unauthorized actions.
Two-Factor Authentication (2FA)
For applications handling highly sensitive data or critical operations, implementing Two-Factor Authentication (2FA) can provide an additional layer of security. 2FA combines something the user knows (e.g., a password) with something the user has (e.g., a mobile device or hardware token) to verify their identity.
Secure Token Management
When using tokens for authentication or authorization, it's crucial to implement secure practices for generating, storing, and validating them. This includes using strong cryptographic algorithms, setting appropriate token expiration times, and securely storing and transmitting tokens to prevent unauthorized access or tampering.
Mitigating SQL Injection and Cross-Site Scripting
SQL Injection Prevention
SQL injection attacks can occur when user input is improperly sanitized and concatenated into SQL queries. To mitigate this risk, always use parameterized queries or object-relational mapping (ORM) libraries like Sequelize or TypeORM, which automatically sanitize user input and prevent SQL injection vulnerabilities.
Cross-Site Scripting (XSS) Prevention
Cross-Site Scripting (XSS) attacks involve injecting malicious scripts into web pages, compromising sensitive data or hijacking user sessions. To prevent XSS vulnerabilities, always sanitize and validate user input before rendering it on the client-side. Use libraries like sanitize-html or DOMPurify to sanitize HTML content and remove potentially harmful scripts.
Securing Sensitive Data with Encryption
Encrypting Data at Rest
Sensitive data stored in databases or file systems should be encrypted to protect it from unauthorized access. Node.js provides built-in support for various encryption algorithms, such as AES and RSA. Additionally, you can leverage external libraries like crypto-js or node-forge for more advanced encryption needs.
Encrypting Data in Transit
When transmitting sensitive data over the network, it's crucial to use secure protocols like HTTPS and SSL/TLS to encrypt the communication channel. This protects the data from being intercepted and read by unauthorized parties.
Key Management and Rotation
Proper key management is essential when using encryption. Follow best practices for generating, storing, and rotating encryption keys securely. Consider using hardware security modules (HSMs) or cloud-based key management services for additional security and ease of key management.
Handling and Validating User Input
Input Validation and Sanitization
User input is a common attack vector for various security vulnerabilities, such as SQL injection, XSS, and Remote Code Execution (RCE). Always validate and sanitize user input before processing it, using libraries like validator or sanitize-html. This ensures that only expected and safe input is processed by your application.
Whitelisting vs. Blacklisting
When validating user input, it's generally recommended to use a whitelisting approach rather than a blacklisting approach. Whitelisting involves explicitly defining allowed input patterns or values, while blacklisting attempts to block known malicious input patterns. Whitelisting is more secure and easier to maintain, as it's impossible to anticipate all potential attack vectors.
File Upload Security
If your application allows file uploads, it's essential to implement security measures to prevent malicious file uploads. This includes validating file types, sizes, and content, as well as securely storing and serving uploaded files to prevent directory traversal attacks or unauthorized access.
Protecting Against Denial-of-Service Attacks
Rate Limiting and Throttling
Denial-of-Service (DoS) attacks attempt to overwhelm your application's resources, making it unavailable to legitimate users. To mitigate this risk, implement rate limiting and throttling mechanisms to control the number of requests a client can make within a given time period. Libraries like express-rate-limit or node-rate-limiter can help you implement these strategies.
Load Balancing and Scaling
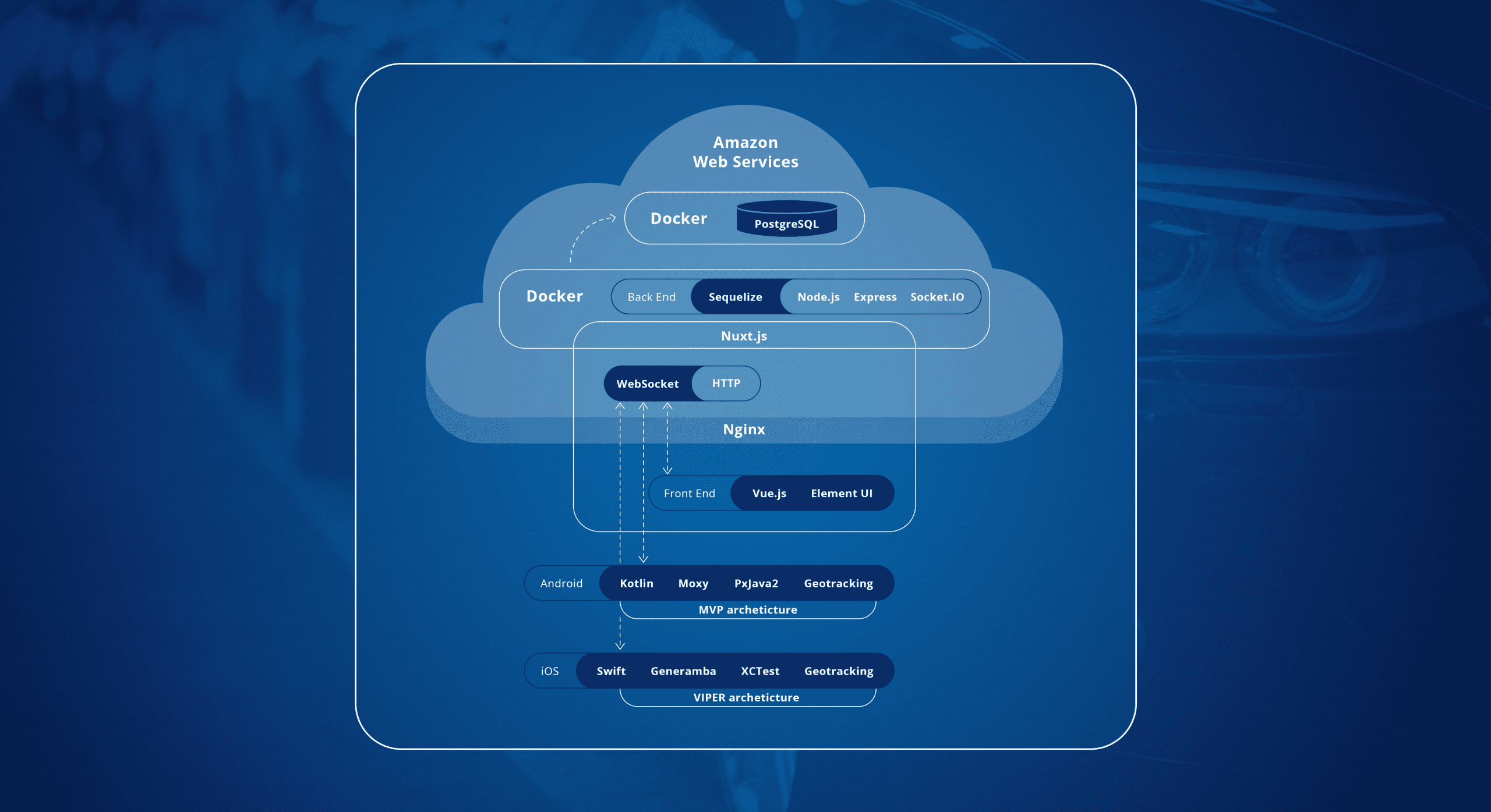
In addition to rate limiting, implementing load balancing and scaling strategies can help distribute traffic across multiple servers and prevent any single server from becoming overwhelmed. Cloud platforms like AWS, Azure, and Google Cloud offer load balancing and auto-scaling services that can be integrated with your Node.js applications.
DDoS Mitigation Services
For high-risk applications or those susceptible to large-scale Distributed Denial-of-Service (DDoS) attacks, consider using a dedicated DDoS mitigation service. These services can detect and filter malicious traffic, protecting your application from being overloaded or taken offline.
Implementing Rate Limiting and Throttling
Rate Limiting Strategies
Rate limiting is a technique used to control the number of requests a client can make within a given time period. This helps prevent excessive resource consumption and mitigate potential Denial-of-Service (DoS) attacks. Node.js offers various libraries and middleware for implementing rate limiting, such as express-rate-limit and node-rate-limiter.
| Library | Description |
|---|---|
express-rate-limit |
A rate limiting middleware for Express.js applications. |
node-rate-limiter |
A flexible rate limiting library for Node.js applications. |
redis-rate-limiter |
A rate limiter that uses Redis as a storage backend. |
Throttling Strategies
Throttling is a complementary technique to rate limiting that controls the maximum number of concurrent requests a client can make. This helps ensure that your application's resources are not overwhelmed by a sudden influx of requests. Node.js libraries like express-throttle and node-rate-limiter can be used to implement throttling mechanisms.
- Use
express-throttlemiddleware for Express.js applications to limit concurrent requests. - Implement token-based throttling with
node-rate-limiterto control request rates based on client identifiers or API keys.
Combining Rate Limiting and Throttling
For optimal protection against resource exhaustion and DoS attacks, it's recommended to combine rate limiting and throttling strategies. Rate limiting can control the overall request rate, while throttling ensures that individual clients do not monopolize your application's resources.
// Example using express-rate-limit and express-throttle
const rateLimit = require('express-rate-limit');
const throttle = require('express-throttle');
const limiter = rateLimit({
windowMs: 15 * 60 * 1000, // 15 minutes
max: 100, // Limit each IP to 100 requests per windowMs
});
const throttler = throttle({
limit: 5, // Maximum 5 concurrent requests per IP
timeoutMs: 60000, // Request timeout after 1 minute
});
app.use(limiter);
app.use(throttler);
In this example, we use express-rate-limit to limit each client IP to 100 requests per 15-minute window, and express-throttle to limit the number of concurrent requests from each IP to 5. By combining these strategies, you can effectively control the overall request rate and prevent resource exhaustion caused by a single client or a group of clients.
Enforcing Secure Coding Standards
Code Reviews and Static Analysis
Implementing secure coding practices is essential for preventing vulnerabilities and ensuring the overall security of your application. Conduct regular code reviews and utilize static analysis tools like ESLint with security-focused plugins to identify and fix potential security issues early in the development process.
Security Linting and Scanning
In addition to static analysis, integrate security linting and scanning tools into your development workflow. Tools like npm audit and snyk can help identify known vulnerabilities in your project dependencies and provide recommendations for remediation. Make security scanning a part of your continuous integration (CI) pipeline to catch issues before they reach production.
Input Validation and Output Encoding
Always validate and sanitize user input to prevent common vulnerabilities like SQL injection and Cross-Site Scripting (XSS). Use libraries like express-validator or joi to enforce data validation rules and sanitize user input before processing it. Similarly, encode output to prevent XSS attacks by escaping special characters when rendering user-generated content.
Principle of Least Privilege
Follow the principle of least privilege when designing your application's architecture and access controls. Limit user permissions and access rights to only what is necessary for their role or function within the application. This reduces the potential impact of a security breach by restricting unauthorized access to sensitive data or functionalities.
Monitoring and Logging for Security
Logging Best Practices
Implement comprehensive logging in your Node.js application to capture relevant security events, errors, and user activities. Log security-relevant information such as authentication attempts, authorization failures, input validation errors, and critical system events. Use structured logging formats and log management tools like Winston or Bunyan for centralized log collection and analysis.
Real-time Monitoring and Alerts
Set up real-time monitoring and alerting mechanisms to detect security incidents and anomalies in your application. Use tools like Prometheus with Grafana dashboards to monitor key performance indicators and security metrics. Configure alerts for unusual activity, high error rates, or suspicious patterns that may indicate a security breach.
Incident Response and Forensics
Develop an incident response plan outlining procedures for identifying, containing, and recovering from security incidents. Define roles and responsibilities for incident response team members and conduct regular tabletop exercises to test the effectiveness of your response plan. Implement forensic logging to capture detailed information for post-incident analysis and investigation.
Continuous Security and Improvement
Security Automation and Testing
Integrate security testing into your CI/CD pipeline to automate security checks and vulnerability assessments. Use tools like OWASP ZAP, Snyk, or SonarQube to scan your codebase for security flaws, compliance violations, and outdated dependencies. Perform regular security assessments and penetration testing to identify and remediate vulnerabilities proactively.
Patch Management and Updates
Stay vigilant about security patches and updates for your application dependencies, frameworks, and operating systems. Monitor security advisories from vendors and open-source communities to stay informed about potential vulnerabilities that may affect your application. Establish a patch management process to promptly apply security patches and updates to mitigate known risks.
Security Training and Awareness
Invest in security training and awareness programs for your development team to educate them about secure coding practices, common vulnerabilities, and threat mitigation strategies. Encourage developers to stay informed about emerging security trends and participate in security conferences, workshops, and certifications to enhance their skills and knowledge.
Video
Conclusion
Securing Node.js and TypeScript back-end applications requires a multi-layered approach encompassing authentication, encryption, input validation, rate limiting, secure coding practices, monitoring, and continuous improvement. By implementing robust security measures and following best practices, you can protect your applications from common threats like SQL injection, XSS, DoS attacks, and data breaches.
Remember that security is an ongoing process, not a one-time task. Stay proactive, keep abreast of security trends, and continuously evaluate and enhance your application's security posture. By prioritizing security from the outset and integrating it into every stage of the development lifecycle, you can build resilient and secure Node.js and TypeScript applications that safeguard sensitive data and maintain user trust."









0 Comments